What’s new in Eficode ROOT: April 2023
The star of Eficode ROOT’s April Extravaganza is deservedly the new SonarQube 9.9 LTS, which is complemented by feature-rich new releases for Jenkins LTS, GitHub Enterprise Server, GitLab and for the JFrog Platform.
The wait was worth it. SonarQube 9.9 LTS is the best SonarQube LTS to date.
No more Java 8
It’s the same old story we’ve heard over and over again during the past year or so: Java 8 is old, and while it once was the greatest creature to roam the earth, evolution is ruthless. It’s only natural that its younger siblings provide the sort of grace, space and pace the eight never could.
With SonarQube 9 it’s time to move on. From this point on, analysis can only be run with Java 11 or later.
If you still happen to have projects set up with Java 8, we highly recommend you check and update the SonarScanner part of them in advance.
When using the standalone SonarScanner from command line or from e.g. Jenkins SonarQube plugin, make sure it is configured to either use System Java or a Java 11 installation. Java 11 is available in all Eficode ROOT CI/CD execution environments.
In the case of SonarScanner for Maven (org.sonarsource.scanner.maven), if your Maven project still needs to be run with an older version of Java, consider migrating to using standalone scanner instead of the Maven plugin, as the SonarQube step will fail.
Picking up the pace
Improving performance has been one of the major objectives of SonarQube 9. Already familiar from our Current series, the LTS also now gains all of the improvements designed to make code analysis happen in a hurry.
There’s a new server-side cache treatment to speed up Pull Request analysis for Java, JavaScript, TypeScript, Kotlin and COBOL, which allows SonarQube to perform PR analysis incrementally by only scanning files changed in the PR. This is proven to improve scan times by 40% on average, with up to 80% reduction seen with larger projects.
All of us with Git-based projects will be pleased to learn that SonarQube 9 makes the first full analysis of a Git codebase up to 60% faster than before through improvements made to blame data retrieval.
Java analysis also benefits from more efficient file handling – instead of processing files one by one, the related files are now handled in batches. An average of 30% improvement in Java Sensor speed has been observed as a result, with larger projects naturally seeing the greatest improvement.
Enterprise Edition users also receive enhanced parallel processing for all languages. The Compute Engine implementation has been updated so that branches will no longer block PR analysis reports from the same project, and different PRs from the same project no longer block each other.
And what’s best: there are no trade-offs. The speed has been achieved by doing things more efficiently than before, without having to make any sacrifices with analysis precision. It’s a win-win situation.
Improving accuracy and precision
The new SonarQube brings lots of new rules, such as those for Kotlin and Java for delivering safe, compliant Android apps.
C and C++ analysis has been updated to make distinction between system and user headers in order to analyze the latter appropriately. This will lead to fewer false negatives for most rules – especially for those advanced bug rules, such as S2259, for detecting null pointer dereferences.
There are also a lot of updates to improve the precision, speed and coverage of the taint analysis engine.
For Android, SonarQube can now provide taint analysis for catching cross-site-scripting, remote code execution, command, SQL and path injections in Java code.
Taint analysis rule descriptions have also been rewritten for Python, PHP, JavaScript and TypeScript to provide deep context and framework-sensitive patch advice. The rule implementations have also been improved for all languages to provide clearer reporting.
Overall, the taint analysis engine will provide rich educational content to make taint analysis rules easy to understand and contextual to your code.
In-depth analysis for creating secure Cloud Native applications
The new LTS delivers static analysis capabilities for development and deployment of Cloud Native applications for the three major cloud providers and their underlying technologies.
For AWS SonarQube can help you deliver a secure infrastructure with new Terraform and CloudFormation rules. There’s also a bundle of new rules to cover the use of AWS CDK in Python and JavaScript/TypeScript, complemented by rules to ensure that your AWS Lambdas are secure and sound.
For Azure and GCP, this release of SonarQube ships with new Terraform rules to help in creating secure infrastructure and application deployments.
There are also new rules to analyze Docker and Kubernetes configuration files to ensure security in containerized deployments.
Updated quality profiles
As is to be expected, the built-in Quality Profiles for all languages get a revision to the latest standards. There may be additions, changes, deprecations or removals of rules for all of them.
If your project is configured to use the provided Sonar Way profiles, you can see the full changelog through the SonarQube UI by navigating to the Quality Profile screen and selecting Changelog.
Further reading
We’ve covered all of these changes in more detail in our earlier release announcements for our Current series back in March 2022, May 2022, August 2022, September 2022, November 2022 and, finally (phew!) February 2023.
We also recommend checking out the Official SonarQube 9.9 LTS announcement on sonarsource.com!
Get Current
With all that said, we would also like to remind you of the possibility of getting more adventurous with SonarQube on Eficode ROOT!
SonarQube Current has been available on Eficode ROOT since January 2022. The Current series delivers the latest SonarQube with all of its changes and features as part of the usual monthly update schedule. Sometimes the world may be on fire after an update, but it may just as well be the best thing ever. Ups and downs, all unfiltered.
Please reach out to your Eficode ROOT Service Manager if you feel like stepping into the world of an early adopter could perhaps just be the ticket for your operation.
A new month, a new GitLab. This month, it’s the version 15.10 with a major SAST improvement.
Auto-resolve SAST findings upon rule removal
When scanning your codebase with SAST analyzers, you’d naturally want the analyzer to provide feedback and results relevant to your project. Sometimes this means modifying the SAST rules, either by disabling predefined rules or by removing rules from the default ruleset.
Previously, when a rule was no longer scanned, findings needed to be manually resolved even though they were marked “No longer detected”. Starting with this release GitLab will now automatically resolve any findings related to the disabled or removed rules, leaving a comment explaining that the finding was resolved due to a rule being not relevant anymore.
This change will also automatically resolve findings from a small number of default rules that have been changed in recent releases of GitLab. GitLab has also removed a “detect-object-injection” JavaScript SAST rule that created an unnecessary amount of false positives.
This feature is enabled by default, but it can optionally be disabled by a GitLab Administrator if it causes problems.
Diagrams for wikis
GitLab 15.10 ships with diagrams.net integration for wikis. It allows you to easily create and edit diagrams for your wiki pages using diagrams.net GUI editor. The feature is available in both the Markdown editor as well as in the content editor.
Lock down SAML SSO groups
This release of GitLab provides the option for GitLab administrators to prevent additional members from being added to groups that are controlled by SAML group links. Before it was possible for a group owner to invite new members to their GitLab group from outside of the SAML synchronization.
By enabling SAML Group Lock you can prevent this. When the lock is enabled, users can only be added using SAML group links.
See the SAML Group Sync documentation on gitlab.com for further details.
And more
As always, this is just a small glimpse of all the changes in GitLab 15.10. Please see the GitLab 15.10 release announcement on gitlab.com for a full and very detailed disclosure on all new features and enhancements in this release of GitLab.
April brings a new feature release of GitHub Enterprise Server - the release 3.8 - with a public beta for Projects, improvements to Actions, audit log and much more.
Projects beta
GitHub Enterprise Server 3.8 ships with the first public beta version of Projects, a flexible tool for planning and tracking work.
A project is an adaptable spreadsheet that integrates with your issues and pull requests to help in planning and tracking your development work. It allows you to create and customize multiple views by filtering, sorting and grouping your issues and PRs, and to add custom fields to track metadata specific to your team.
Projects doesn’t enforce a specific methodology, but provides flexible features you can customize to tailor the project to fit your team’s needs.
Interested? Check out About Projects (beta) on github.com for more! Please note that since the feature is currently in its beta stage, it is still subject to change.
More advanced audit trail
Starting with this release of GitHub, enterprise owners can now more easily detect and trace activity associated with authentication tokens by viewing token data in audit log events. It’s also now possible to stream audit log events into a Datadog endpoint.
There’s also a new option to review and revoke both browser and GitHub Mobile sessions for your user account. You can view all active sessions for your account in the “Access” section of your user profile Settings page.
Actions enhancements
This release of GitHub brings general availability for the ability to share actions and reusable workflows from private repositories. You can share workflows in a private repository with other private repositories owned by the same organization or user account, or with all private repositories in the GitHub instance.
GitHub allows you to control access to runners within an organization using runner groups. It is possible to have runners with the same labels in multiple different groups, which means your job could have ended up on a runner in a different group than intended. Now it’s possible to define the names of the runner groups by defining groups within the runs-on key. Please see Choose a runner for a job on github.com for an example setup.
For cloud deployment workflows using OIDC configurations, it is now possible for organization owners and repository administrators to customize the standard subject claims to suit your required access conditions. You can leverage OIDC and the new customization options to better integrate your workflows with HashiCorp Vault, for example.
Improved repository permissions and much more
You can also now avoid granting full administrative access to a repository, when you only need to allow users to bypass branch protections. Repository administrators can now create a custom role to allow just that.
It’s also possible to further enforce branch protections for all users, even those with administrative access or bypass permissions. To do so, select the Do not allow bypassing the above settings flag for a branch protection rule.
Our highlights here merely represent a small portion of the changes and enhancements in GitHub Enterprise Server 3.8. Be sure to check out the Release Notes for 3.8 on github.com for a complete overview.
In April Jenkins gets a brand new LTS release 2.387.1 with some notable changes.
UI modernization, part n+1
The modernization effort of Jenkins UI continues with this LTS, with updates to various UI elements.
The System Information page has been improved by moving from a massive single-page display to separate tabs for different sections. The potentially sensitive values are now also hidden by default, to enhance security of Jenkins.
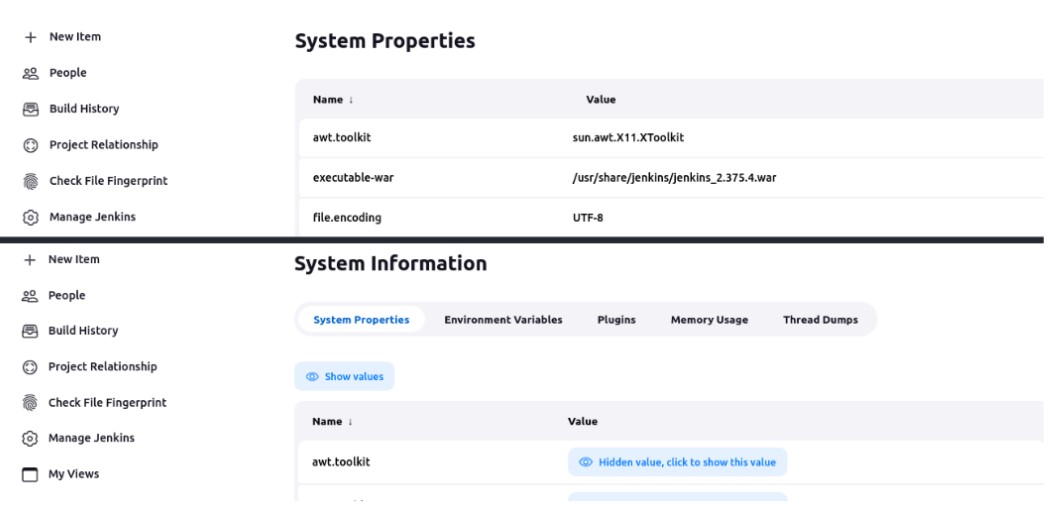
Top: System Properties in Jenkins 2.375.4 LTS, bottom: new System Information screen in 2.387.1 LTS.
The old YUI tooltips have also been replaced with new implementations based on Tippy.js. Not only does the new framework allow for greater flexibility for developers for providing accurate, on-point tooltips, it also improves on the usability and appearance of existing tooltips for us mere mortals.
There are also various enhancements to table displays, button appearance, page layouts and so forth, to make Jenkins UI more coherent and easier-to-use.
Other changes and improvements
This release also ships with a host of other fixes and enhancements to the Jenkins Core, such as:
- Several fixes and improvements to WebSocket agent connections, for improved stability.
- Enhancements to the Plugin Manager.
- Update to Spring Security version 5.8.0 to correct CVEs affecting the previous 5.7.4.
- Robustness improvement for possible build number collisions.
- And much more. Please see the Jenkins LTS Changelog on jenkins.io on nitty-gritty details.
Naturally we also ship the usual monthly round of plugin updates, which this time mostly revolves around the recent discontinuation of Java 8 support in Jenkins Core: many plugins get a bit of a refresh by dropping old Java 8 code and the compatibility with old Jenkins Core versions.
Unique snowflakes as they are, the full list of plugin changes is slightly different from Jenkins to Jenkins. As always, please reach out to your friendly Eficode ROOT Support if you’re interested in the list of changes specific to your own snowflake.
The April Eficode ROOT Release also ships with goodies for the JFrog Platform, in the form of Artifactory version 7.55.8 and Xray version 3.69.3.
Artifactory
Readme tab in package information
Have readme files in your packages? So do we. And those readmes often exist for a good reason too.
The new package information Readme tab in Artifactory 7.55.8
This month we’re in for a treat: no more downloading of artifacts just to view their documentation!
Artifactory 7.55.x makes better use of the readme content by introducing a new Readme tab in the WebUI, which allows viewing the readme files inside PyPi, npm, NuGet, Cargo, CRAN, Helm and Swift packages directly in Artifactory package information view. Oh, how convenient.
In other news
This release of Artifactory also includes various additions related to managing Release Bundles.
There’s a new retention policy feature for Release Bundles received in Artifactory. The policy can be configured to run automatically or on-demand using new Retention APIs (link to jfrog.com). In addition to the “usual” retention policies, it also includes an option to mark Release Bundles as “keep”, which will block any attempts (REST API or UI) of removing the protected Release Bundle.
In addition, there’s a new Cleanup Report for Received Release Bundles available in the JFrog Platform UI, which allows administrators to manage and delete Release Bundles directly from the UI. All cleanup actions are then recorded in the new Cleanup History function for an audit trail. Check out the Documentation for Managing Release Bundles on jfrog.com for more details.
As per usual, a complete overview of all changes and fixes in this release of Artifactory can be found on Artifactory Release Notes on jfrog.com.
Xray
Improved Jira integration
The Jira Integration has been further improved in this release of Xray. It now supports creating Jira tickets manually for any violation from the comfort of Xray UI.
There are also other improvements, such as:
- A new icon that is displayed next to all violations to indicate whether there’s a Jira ticket attached to it.
- Enhancements to the Jira ticket structure to include details on Operational Risk, License violations and on Regular and High profile security vulnerabilities.
- Improvement to Jira ticket creation for having only one ticket for all the information regarding all affected components, instead of having separate tickets for each component.
Usability improvements for the UI
The Scans List UI has received improvements and enhancements to the Vulnerabilities and Exposures categories screens.
For the Vulnerabilities screen, default displayed columns and column ordering have been improved. The default sorting has been modified by adding a secondary sort key by applicability result. There are also new sorting options that have been added for different columns.
The Exposures categories screen is now split into two distinct tabs: To Fix and Checked OK. Issues that were checked and found OK are moved to their own tab, helping you to focus on the important stuff.
There are also new tooltips in the navigation bar to help explain each of the security issues screens.
Other additions and enhancements
This release of Xray adds the support for performing scans on Cargo packages (Rust Crates).
To help you reduce exploitability risks, a SBOM can now be exported from Xray with CycloneDX VEX (Vulnerability Exploitability eXchange) information, such as vulnerability details, exploitability and detailed analysis.
Published:
Updated:


