Security and Devops

Two words: Security and Devops. This blog jumps in time to the DEVOPS 2016 and very interesting topic of SecOps.
On first day of Devops 2016 the topic of security in Devops processes was picked up by Jani Kirmanen from Silverskin and Visa Parviainen from Eficode. Their presentation had two parts to offer different points of the topic.
The talk was started by Kirmanen, who is a specialist in cyber security. Right at the beginning he introduced Silverskin as “a cyber attack company”, and said he will talk about security in terms of offense.
He started with a series of “O RLY?” parody images to illustrate how bad software is created. The included here images seem like some of the most obviously bad practices that happen in the industry.
Why exactly are they so bad? It is because they create the unknowns, Kirmanen said. With them, the project turns into a black box of badly tested, illegible code with redundant libraries. Top it off with missing documentation and nobody on the team will be able to guess how secure it is. To reverse this, the whole team needs to get together and build their knowledge about the system. It can be a lot of effort, but Kirmanen explained neatly the necessary steps.
Once the team learns all about the system, they can start testing it. This too can be tough. Aside from testing what you have, you also need to find what is not there. For example, security holes can be missing exception handlers. Such uncaught exceptions can be dangerous, so once found they need to be handled in code and tested. It is not the end though. If the product is in continuous development, search for security holes will also have to continue. Kirmanen advised adding it as a step to the agile iterative process.
With this advice, Kirmanen finished his side of the story on how to improve security in a project. At this point, Parviainen took over the microphone.
He started his talk by discussing structural analysis of a web service. He listed the elements on the slides neatly, with their general vulnerabilities and how to deal with them. His emphasis was on tools and automatization. One such analysis example is attached below. It shows the infrastructure’s security issues and how to remedy them.
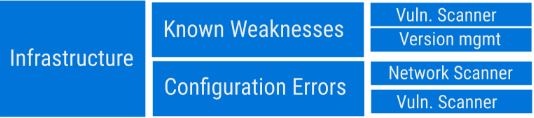
The complete list in the last slide was quite long, detailing all the pieces of the example service. The amount of material was quite large, so he had to speak quite fast to finish his presentation in time.
Looking back at the talks, both presentations complemented each other. First part was mostly about investigative group work, while the second was a tidy dissection of a service and analysis of what could be automated there. Both had slides packed with information and detailed diagrams. They could be used to kick-start security improvements in almost any software project.
Aside from the quality of the talks, what got my attention was Kirmanen’s viewpoint on security. How common it is to hear in the industry that the best form of security is attack? Most development teams probably do not want to think about attacking their software. Unfortunately, missing the attacker’s point of view might hold them back from producing really secure software.
To see this 2-part talk, follow the link.
Interested in data security? Eficode and Silverskin have published a security guide.
Published:
Updated:

